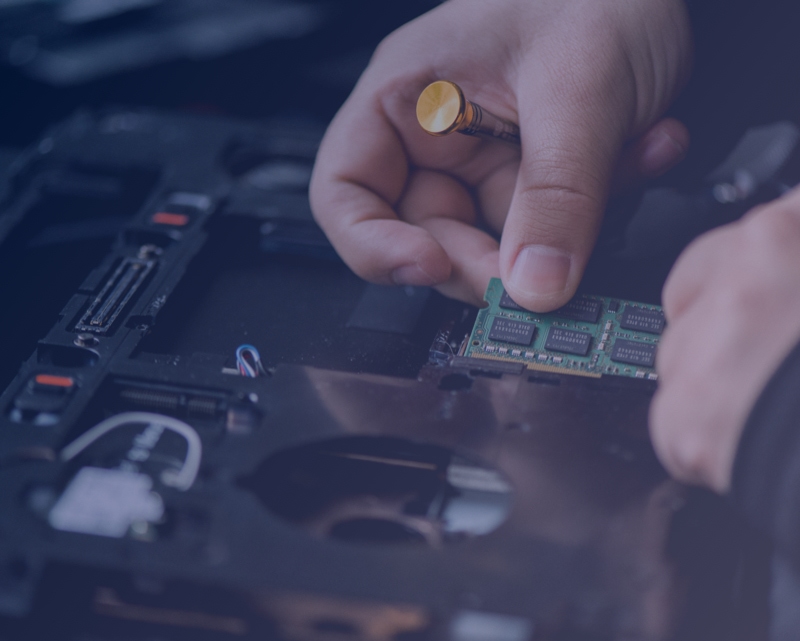
Managed IT Services You Can Trust
Approach
Fully-Managed One-Stop Solution
From Research, Assessment, Planning, Procurement, Delivery, Installation, we provide end to end solutions for all your IT & Sales requirements
Approach
Cost Effective Solutions
By studying your business requirements and recommending only the equipment/configuration that you really need, we help you save cost
Approach
Ease of Business
We believe in simplicity & hassle-free business operations. Our focus is always on quality, reliability & we find the most effective solutions
SERVICES
What We Do
IT Infrastructure Solutions
Prepare to be an agile, high-performance and secure IT infrastructure with Genome…

NEW OFFICE SETUP
Creating a robust plan and setup your new office IT infrastructure. Having helped setup numerous…

HOME NETWORK SETUP
Internet has transformed into a necessity today; be it office or home. With home automation on…
STRUCTURED CABLING
Genome is backed by the most experienced and dedicated team of network engineers for…

Enterprise Solutions
Genome, enables you to leverage emerging technologies through our enterprise solutions encapsulated…
COLLABORATION
Communication & Collaboration creates an environment where people can work effectively…
STORAGE
Finding and managing multi disk drives becomes increasingly difficult as the need for data storage…
CONTACT CENTRE SETUP
Genome offers you unified contact center enterprise solutions that will deliver intelligent contact routing..
We Create Fully Connected Systems So You Can Focus On Your Business
Get Started
Technology Partners








Contact Us!
Office
#311, 3rd Floor, Al Zarouni Business Centre - Al Barsha 1 - Dubai - United Arab Emirates
Call Us
+971 4 370 8091
